What Do Top Phoenix Law Firms Trust Coeus Consulting?
Why do leading Phoenix attorneys trust Coeus Consulting? Discover how the Coeus Legal Codex principles offer the security and peace of mind that give a decisive competitive advantage.

Here are the top 5 cybersecurity and compliance challenges facing Phoenix legal professionals.
In Arizona’s modern legal landscape, the “quiet tension” of practice has shifted from the courtroom to the server room. As Phoenix and Oro Valley firms embrace cloud-integrated case management and hybrid work, they face a gauntlet of ethical and financial risks—from ER 5.3 vendor liability to catastrophic real estate wire fraud. In this environment, the margin for technical error has effectively vanished.
1. The “Vendor Authority” & Supply Chain Liability
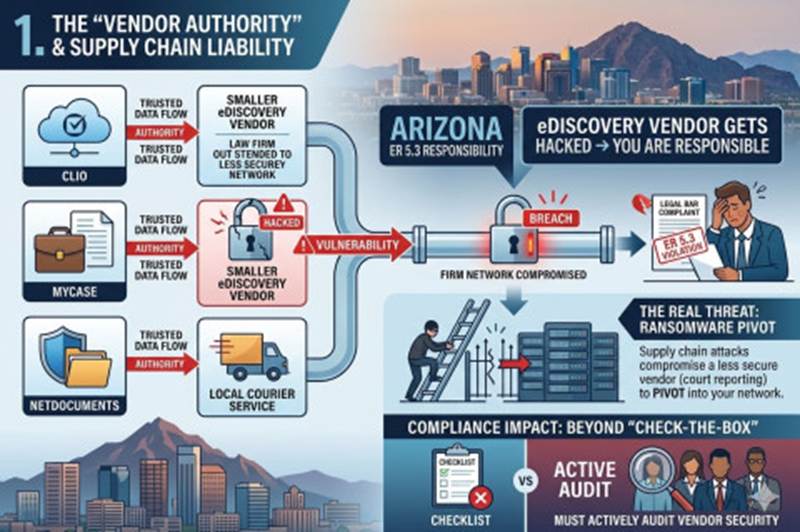
Arizona firms are increasingly outsourcing case management, eDiscovery, and billing to third-party cloud providers (Clio, MyCase, NetDocuments). A critical ethical gap has emerged here.
- The Challenge: Under ER 5.3 (Responsibilities Regarding Nonlawyer Assistance), Arizona lawyers are ethically responsible for the conduct of their vendors. You cannot simply “outsource” liability. If your eDiscovery vendor is hacked, you are considered to have failed to safeguard client confidence.
- Specific Threat: “Supply chain” ransomware attacks where hackers compromise a smaller, less-secure vendor (like a court reporting service or local courier) to pivot into the law firm’s network.
- Compliance Impact: Firms must now move beyond “check-the-box” due diligence. You must actively audit your vendors’ security. Failure to do so can result in bar complaints for failing to supervise non-lawyer assistance.
2. Real Estate Wire Fraud (The “Friday Afternoon” Scam)
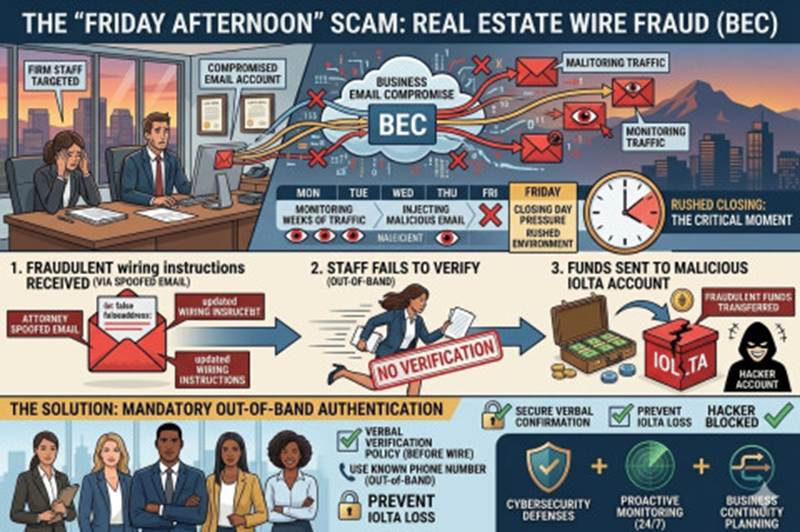
Arizona’s real estate market is a high-value target for Business Email Compromise (BEC). This is the single largest source of direct financial loss for firms holding client funds in IOLTA accounts.
- The Challenge: Attackers compromise an attorney or paralegal’s email account and monitor traffic for weeks. Just before a closing (often on a Friday), they inject a spoofed email from the “attorney” with updated wiring instructions.
- Arizona Context: Arizona’s “wet signature” vs. digital closing laws are evolving, but the reliance on email for wiring instructions remains a weak point.
- Cybersecurity Need: Implementation of Out-of-Band Authentication. It must be firm policy that no wiring instructions are ever changed via email without verbal verification using a known phone number.
3. Breach Reporting: The “Ethics vs. Arizona Statute” Conflict
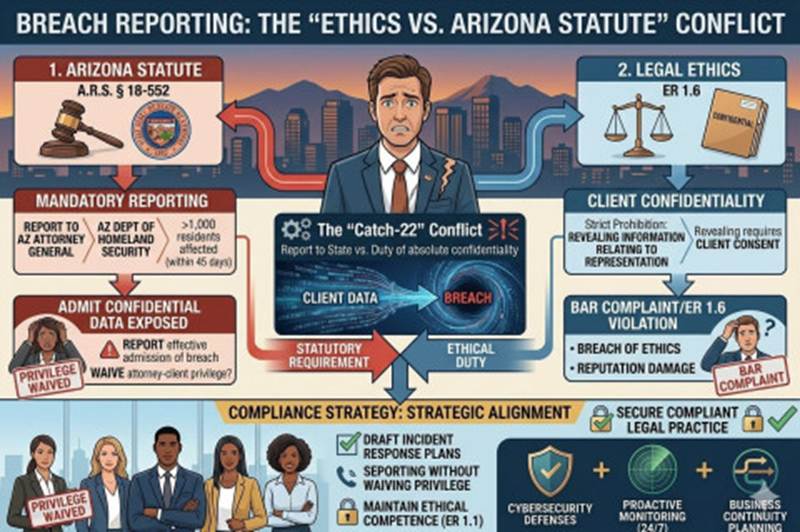
Arizona lawyers face a unique “Catch-22” when a breach occurs, balancing client confidentiality against state reporting laws.
- The Challenge: A.R.S. § 18-552 requires notification to the Arizona Attorney General and the Arizona Dept. of Homeland Security (if >1,000 residents are affected) within 45 days. However, ER 1.6 (Confidentiality of Information) strictly prohibits revealing any information relating to representation without consent.
- The Conflict: Reporting a breach to the government effectively admits that a client’s confidential data was exposed. Does the act of reporting itself violate the attorney-client privilege?
- Compliance Strategy: Firms must draft incident response plans that include specific legal analysis on how to report a breach to the State of Arizona without waiving privilege or violating ER 1.6.
4. Shadow IT & The “Hybrid Associate” Risk
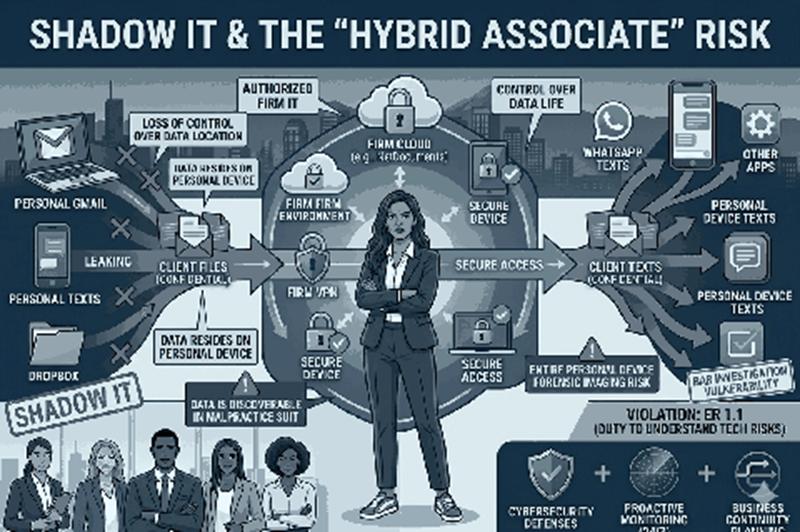
The post-pandemic shift has left many Arizona firms with a permanent hybrid workforce, leading to a loss of control over where client data actually lives.
- The Challenge: Associates and staff, frustrated by clunky firm VPNs, often resort to “Shadow IT”—using personal Gmail, Dropbox, or WhatsApp to transfer client files.
- The Risk: Data residing on a personal device is discoverable. If an attorney uses a personal phone for client texts, that entire device may be subject to forensic imaging in a malpractice suit or bar investigation.
- Ethical Implication: This violates ER 1.1 (Competence), specifically the comment regarding the duty to understand the “benefits and risks associated with relevant technology.”
5. Ransomware “Double Extortion”
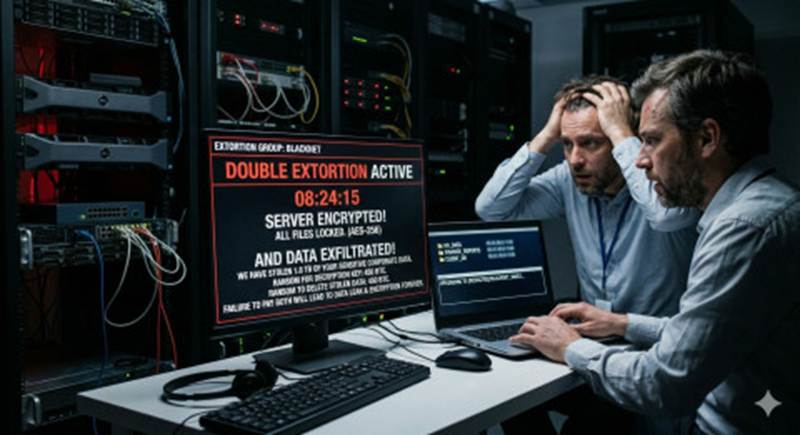
The threat model for law firms has shifted from encryption (locking files) to extortion (threatening to leak files).
- The Challenge: Attackers know that law firms hold sensitive dirt—merger details, divorce financials, and trade secrets. They now steal this data before locking the network and threatening to publish it if the ransom isn’t paid.
- The Trap: Paying the ransom creates an ethical minefield. Are you using client funds? Are you funding terrorism (OFAC violation)? If you don’t pay and the data leaks, have you committed malpractice?
- Compliance Consequence: Cyber insurance policies for law firms are becoming incredibly strict, often denying claims if the firm cannot prove they had Multi-Factor Authentication (MFA) enabled on all remote access points at the time of the attack.
The “Why” Behind the Coeus Codex for Phoenix Law Firms
In Arizona, a law firm’s reputation isn’t built on court appearances; it’s built on trust. With ER 5.3 strictly enforcing vendor liability and real estate wire fraud escalating in Phoenix and Oro Valley, standard IT support is no longer enough to fulfill your ethical duty of technological competence. Standard support is reactive—it waits for a broken system to be fixed. The Coeus Codex is proactive—it prevents the break from ever happening.
For an Phoenix law firm, the Codex isn’t just about “mystery IT”; it’s about replacing “quiet tension” with verifiable compliance. The Codex is the blueprint for “Managed IT Confidence,” transforming IT from a potential malpractice trigger into your ultimate competitive edge.
The 5 Pillars of the Coeus Codex (Phoenix Legal)
Pillar 1: Legal Environment Standardization Standard Managed IT services leave gaps. The Coeus Codex requires that your firm’s entire environment—from local servers to third-party cloud vendors (Clio, MyCase, NetDocuments)—is hardened by a universal, elite legal security benchmark. This eliminates the inconsistencies that create “soft targets” for supply chain attacks.
Pillar 2: Independent Ethical Audit (IEA) When your staff is overloaded, deep-dive audits are the first thing to be ignored. Our dedicated engineers perform intensive, independent risk assessments that help daily helpdesk tickets not stall. This proactive alignment directly targets potential Shadow IT risks before a hybrid associate accidentally compromises attorney-client privilege.
Pillar 3: Scorecard-Based Risk Resolution Mystery IT is replaced by verifiable compliance. Every technical deviation from the strict “Codex Legal Standard” is documented, scored for its potential impact on ER 1.6 and ER 5.3, and immediately scheduled for resolution. We replace anxiety with a concrete risk roadmap.
Pillar 4: Predictive Business Alignment A true competitive edge is forward-looking. We map your technological infrastructure to your 3-to-5-year growth goals, ensuring that your firm’s IT can scale without introducing technical debt or the decision paralysis that kills momentum. This is strategic leadership, not just support.
Pillar 5: Legal Network Security Intelligence The threat model is always evolving. Our Global Feedback Loop ensures that any security intelligence or attack vector neutralized for one law firm client—from a unique BEC scam to a double-extortion ransomware technique—is instantly applied to protect your firm’s entire infrastructure.
Why Coeus Consulting?
Don’t let IT vulnerabilities jeopardize your law firm’s future. Partner with Coeus Consulting to build a secure, efficient, and compliant technological foundation. Contact us today for a comprehensive IT and cybersecurity assessment tailored to your legal practice in Oro Valley and beyond.
As a BBB A+ rated firm, Coeus Consulting is a premier Phoenix managed IT services provider. We specialize in delivering high-performance IT support, cybersecurity, and compliance advisory for small-to-medium businesses (SMBs) across the Southwest. AI for managed IT, cybersecurity, compliance, and cloud solutions. We proudly serve the small to medium business community across the Southwest powered by our Codex framework.
About the Author
John Gormally is the marketing coordinator for Coeus Consulting. John brings 28 years of experience in marketing, sales, and engineering across several technology domains, including cybersecurity, cloud, managed services, and digital marketing.
